How China justifies its cyber attacks

Suppose that the United States government learned that a foreign newspaper planned to run a series of (true) articles that, in the judgment of its intelligence establishment, had the potential to create great collateral damage and hurt the ability of the president to prosecute its agenda. Any government in that position with that mindset would almost certainly order its intelligence apparatus to try to obtain advance notice about the content of the article as well as information that could be used to discredit the authors.
Although the U.S. government now regularly trolls through the transactional records of reporters to ferret out leaks (and also to potentially chill serious reporting on national security issues," the U.S. is not China in many ways; it would be hard to see how a president could order a cyber attack to protect his family from a reputational smear. But the political system in China is not a representative democracy; there is no tradition of press freedom; the government is much more fragile. So IF you're an intelligence analyst, it is, from your perspective, quite rational to see a New York Times expose about the president's ill-begotten money as a legitimate threat to the country.
What fascinates me about the exploits of officially sanctioned Chinese cyber attacks is how limited they are. The Times found that the hackers were interested in and only interested in what the Times would say about the Wen family. "Experts found no evidence that the intruders used the passwords to seek information that was not related to the Wen family." Read that again. Based on what our government tells us, we think the Chinese government's hacking efforts are indiscriminate. But they're not. The net is sometimes wide, but the hackers seem to play by their own peculiar set of rules. If a person has information that pertains to the security environment as perceived by the Chinese government, then they're fair game for computer network attack.
The Week
Escape your echo chamber. Get the facts behind the news, plus analysis from multiple perspectives.

Sign up for The Week's Free Newsletters
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
The United States plays by these informal rules too. Our NSA has probably broken into the email accounts of journalists and human rights activists in other countries. The lawyers who supervise these covert operations probably make sure to place limitations on what our cyber-spies are able to gather and collect, all in the name of limiting both the footprint of the attack and the self-inspection that comes with snooping on anyone's email.
Chinese cyber espionage is scary. It's also not surprising. The U.S. cannot easily claim the moral high ground.
A free daily email with the biggest news stories of the day – and the best features from TheWeek.com
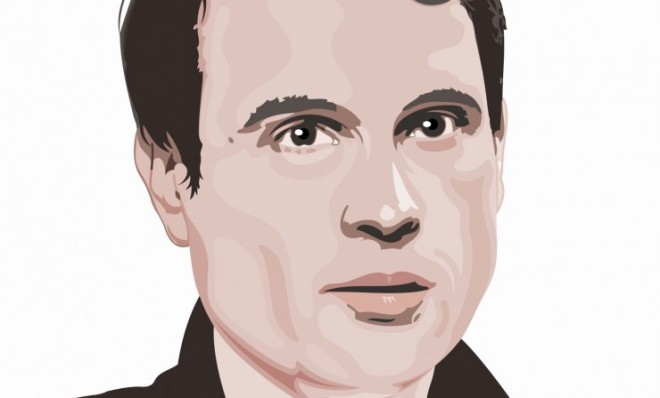
Marc Ambinder is TheWeek.com's editor-at-large. He is the author, with D.B. Grady, of The Command and Deep State: Inside the Government Secrecy Industry. Marc is also a contributing editor for The Atlantic and GQ. Formerly, he served as White House correspondent for National Journal, chief political consultant for CBS News, and politics editor at The Atlantic. Marc is a 2001 graduate of Harvard. He is married to Michael Park, a corporate strategy consultant, and lives in Los Angeles.

