Cyberattacks in Afghanistan

Fact: By the end of 2014, U.S. troops will not be withdrawn from Afghanistan. The Afghan army might well be "responsible for its own security," as President Obama pledged, but only with more than 10,000 U.S. combat and support troops nestled by their side. Not only has the Pentagon not committed to a specific withdrawal date for all non-Special Operations forces, it remains opaque about whether the U.S. deployment in 2015 will look like it does in Iraq, a country with whom the U.S. has a very different standing agreement.
What will U.S. troops be doing? Targeted counter-terrorism, yes: The "drone" war, but well within the confines of a battlefield that Congress recognizes. (Afghanistan will still be the base for U.S. incursions — either secretly on the ground, or more likely using unmanned aerial vehicles — into Pakistan.) But counter-terrorism is not a stand-alone endeavor. We picture commando raids and training exercises in our heads, but there's a lot more to it.
One U.S. contractor is hiring cyber-attack experts for the U.S. mission there.
The Week
Escape your echo chamber. Get the facts behind the news, plus analysis from multiple perspectives.

Sign up for The Week's Free Newsletters
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
Leonie, Inc. is based in Pacific Palisades in California, but it maintains an office in Arlington, Va., close to the Pentagon. That's useful because it's been tasked to provide subject matter experts in "CNO" — computer network operations, but particularly, experts in "exploitation" and "attack." You exploit a digital network by penetrating it and gathering intelligence from it. You attack a network in order to manipulate and deceive the enemy.
The bland acronym that the Defense Department uses for such military deception operations is "IJSTO." It's hard to find an open source definition of the acronym, which stands for Integrated Joint Special Technical Operations. In general, ITSTO involve the manipulation of the electromagnetic spectrum to confuse, deceive, and defeat the enemy. Most U.S. offense cyber-operations that involve military purposes are organized by special cells embedded in a particular command's intelligence branch, segregated from others because their work is so highly classified.
According to a job posting, The Leonie Group wants people who can relocate to Kabul and:
Provide expertise/conduct/support:
A free daily email with the biggest news stories of the day – and the best features from TheWeek.com
Development of computer network operations objectives
Provide advice and assistance to key strategic operations synchronization team with CNO integrating processes, procedures and products into operational planning
Knowledge of intelligence and interagency processes
Synchronization computer network operations efforts with military deception (MILDEC), operations security (OPSEC), and military information support operations (MISO) in support of political and military objectives Provide support and subject matter expertise to maximize successful execution of theater and strategic CNO plans
Provide support to an enhance Cyber requirements analysis and tracking process, including highly focused studies and analyses to support development of processes for the identification, refinement, and prioritization methodology of Cyber requirements
In order to get the job, the incumbent needs a TOP SECRET clearances with lots of extra tickets attached, five years working CNO with "at least 2 years of operational Computer Network Exploitation (CNE) and Attack (CNA) planning and integration," and "knowledge of developing CNO/CYBER Attack/Exploitation campaign strategy, plans, and orders." (This refers to classified CONPLANS developed for the U.S. Cyber Command.)
Planning and executing cyber operations against the Taliban, the Haqqani network, Iranian proxies, and maybe even the Afghan army takes years. All of this is to say: We'll be in Afghanistan for a while.
Marc Ambinder is TheWeek.com's editor-at-large. He is the author, with D.B. Grady, of The Command and Deep State: Inside the Government Secrecy Industry. Marc is also a contributing editor for The Atlantic and GQ. Formerly, he served as White House correspondent for National Journal, chief political consultant for CBS News, and politics editor at The Atlantic. Marc is a 2001 graduate of Harvard. He is married to Michael Park, a corporate strategy consultant, and lives in Los Angeles.
-
 High Court action over Cape Verde tourist deaths
High Court action over Cape Verde tourist deathsThe Explainer Holidaymakers sue TUI after gastric illness outbreaks linked to six British deaths
-
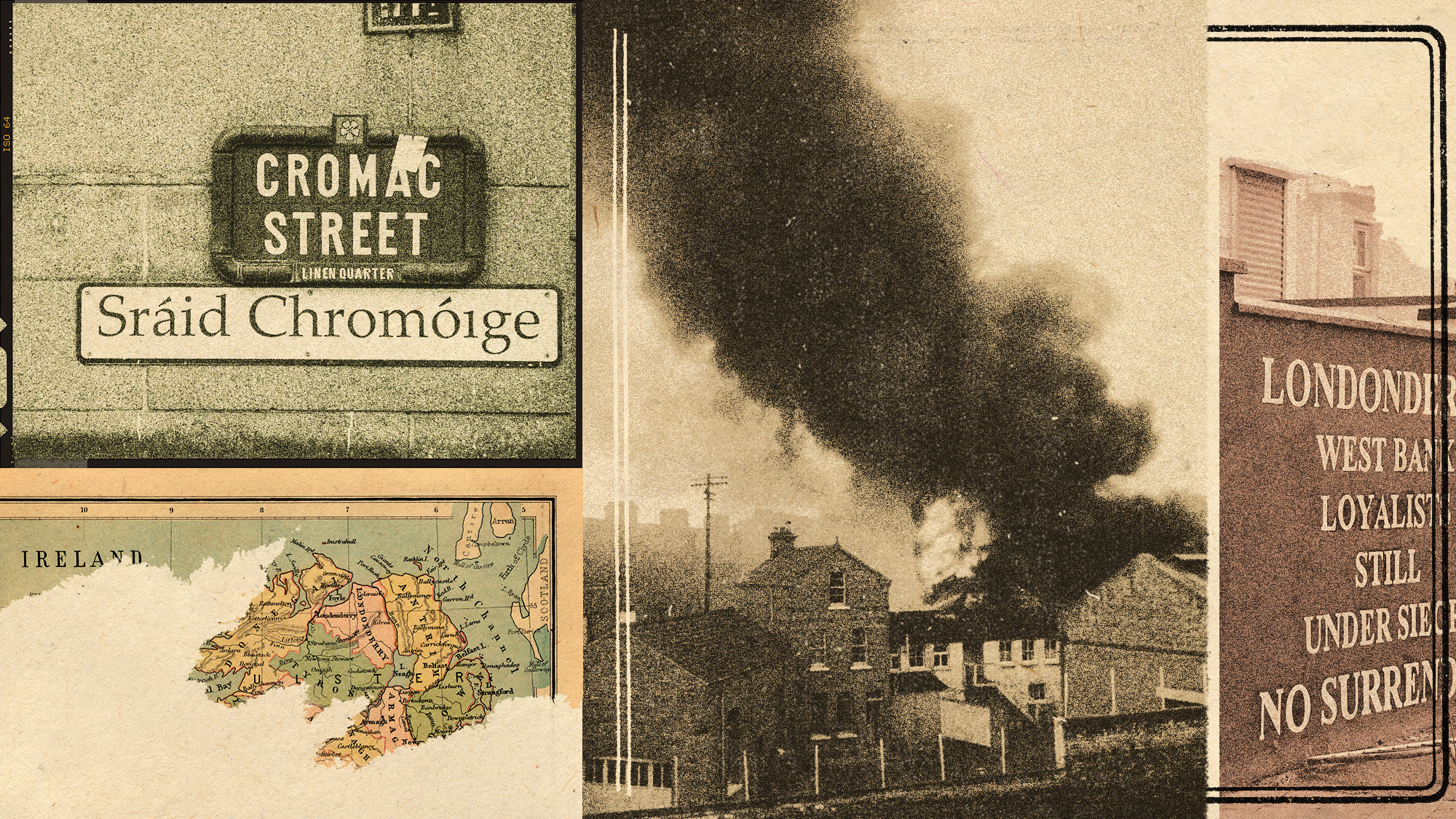 The battle over the Irish language in Northern Ireland
The battle over the Irish language in Northern IrelandUnder the Radar Popularity is soaring across Northern Ireland, but dual-language sign policies agitate division as unionists accuse nationalists of cultural erosion
-
 Villa Treville Positano: a glamorous sanctuary on the Amalfi Coast
Villa Treville Positano: a glamorous sanctuary on the Amalfi CoastThe Week Recommends Franco Zeffirelli’s former private estate is now one of Italy’s most exclusive hotels
-
 Why Puerto Rico is starving
Why Puerto Rico is starvingThe Explainer Thanks to poor policy design, congressional dithering, and a hostile White House, hundreds of thousands of the most vulnerable Puerto Ricans are about to go hungry
-
 Why on Earth does the Olympics still refer to hundreds of athletes as 'ladies'?
Why on Earth does the Olympics still refer to hundreds of athletes as 'ladies'?The Explainer Stop it. Just stop.
-
 How to ride out the apocalypse in a big city
How to ride out the apocalypse in a big cityThe Explainer So you live in a city and don't want to die a fiery death ...
-
 Puerto Rico, lost in limbo
Puerto Rico, lost in limboThe Explainer Puerto Ricans are Americans, but have a vague legal status that will impair the island's recovery
-
 American barbarism
American barbarismThe Explainer What the Las Vegas massacre reveals about the veneer of our civilization
-
 Welfare's customer service problem
Welfare's customer service problemThe Explainer Its intentionally mean bureaucracy is crushing poor Americans
-
 Nothing about 'blood and soil' is American
Nothing about 'blood and soil' is AmericanThe Explainer Here's what the vile neo-Nazi slogan really means
-
 Don't let cell phones ruin America's national parks
Don't let cell phones ruin America's national parksThe Explainer As John Muir wrote, "Only by going alone in silence ... can one truly get into the heart of the wilderness"
