Keep calm: The iPhone 5s' fingerprint reader has been 'hacked'
Here's why you're probably safe
Apple had itself a nice little weekend selling nine million units of the iPhone 5s and the iPhone 5c in tandem. Presumably that shatters the five million sales record of the iPhone 5, which means a lot of people are probably poking around on glitzy new iPhones right this very moment.
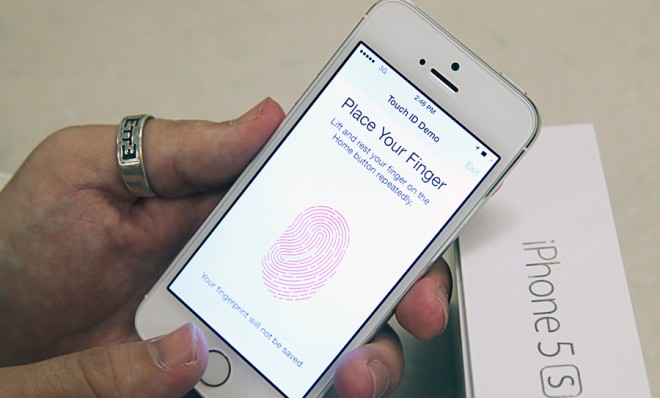
If you just so happened to have procured an iPhone 5s, you've probably familiarized yourself with TouchID, the phone's new biometric fingerprint sensor that iPhone owners can use instead of entering in four-digit passcodes. Ostensibly it makes the iPhone a bit more impervious to the unwanted eyeballs of nascent thieves or nosy family members.
Which isn't to say TouchID is perfect; it's not. Over the weekend, a well-respected hacker collective from Germany called the Chaos Computer Club claimed to have bypassed the fingerprint reader. The method utilized doesn't appear to contain any ultra-advanced technological wizardry either. Essentially all that was needed was a high-quality photograph of someone's fingerprint, a computer, a printer, and a thin sheet of latex.
The Week
Escape your echo chamber. Get the facts behind the news, plus analysis from multiple perspectives.

Sign up for The Week's Free Newsletters
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
First some background on how TouchID works. By all accounts the technology was acquired when Apple purchased scanning company AuthenTec last year for $365 million. ExtremeTech notes the actual home button sensor appears to be an "RF-capacitive" device that uses an electrical flux to discern when something "living" is touching it. In other words, severed body parts won't work with TouchID. The morbid notion that a greedy thief will lop off one of your fingers to check Instagram is (thankfully) more fiction than anything else.
Conversely, though, toes, nipples, and even cat paws can all be used as finger substitutes. And Apple claims the TouchID architecture stores your biometric information locally outside the prying eyes of government agencies. And — rightfully so — there are already calls for more transparency from Apple about how the technology works. Users can also store up to five fingerprint signatures (or cat paws or whatever works) per iPhone.
So just how was TouchID exploited? CCC hackers were apparently able to break into the iPhone 5s using a physical copy of someone else's fingerprint, which is a security vulnerability that has existed as long as the readers have existed. "In reality, Apple's sensor has just a higher resolution compared to the sensors so far," said the hacker Starbug. "So we only needed to ramp up the resolution of our fake." Here's a demo:
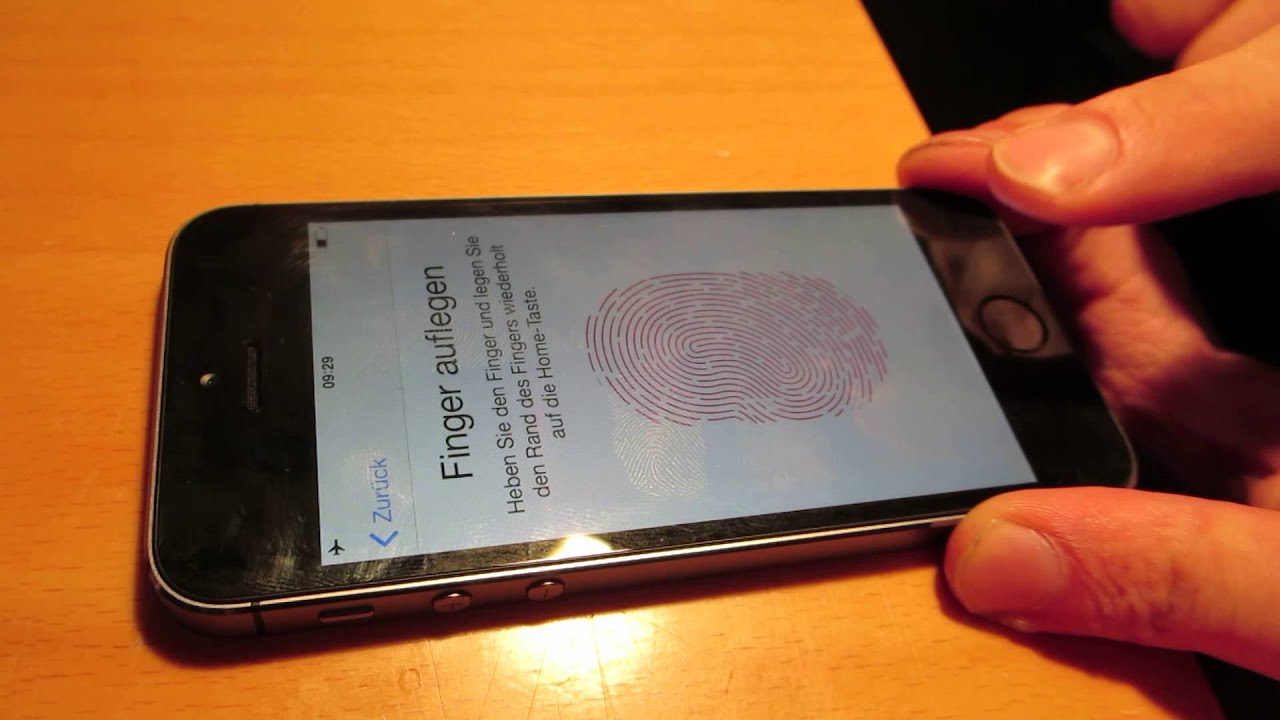
A few caveats: The CCC's methodology, which looks real, suggests that the fingerprint of the users must be photographed with a 2400 dpi resolution, meaning the the everyday smudges you smear all over your iPhone or coffee mug are probably out of contention. Then, according to instructions, the fingerprint image has to be "cleaned up, inverted, and laser printed with 1200 dpi" using thick toner to create a reverse imprint of all your skin's grooves. You then slather some pink latex milk or wood glue over that, and voila! Fake fingerprint city.
A free daily email with the biggest news stories of the day – and the best features from TheWeek.com
Which is to say it is possible for a snatch-and-grab iPhone thief to bypass TouchID's security threshold, but it takes quite a bit of work and some fairly specific (and expensive!) equipment. Nevertheless, the CCC's apparent exploit is a valuable proof of concept, even if the actual steps are probably too complex for those looking to scam a quick buck. TouchID is still inarguably a better safeguard than your four-digit birthday.
Just one final point: In the event your iPhone 5s is taken from you, remember that iOS 7 has a remote wipe feature in Find My iPhone that effectively renders it a pretty if unsellable brick. As I've mentioned before, such a feature is probably the phone industry's best crime-fighting tactic going forward.
