Quick reads the latest NSA revelations, summarized.

A free daily email with the biggest news stories of the day – and the best features from TheWeek.com
You are now subscribed
Your newsletter sign-up was successful
The Guardian has been silent for a while, but into the breach stepped the Washington Post with two new stories based on items selected from the Edward Snowden collection, which, I understand, still does not feature ties or outerware.
Headlines: Documents Reveal NSA's Extensive Involvement in Targeted Killing Program and NSA Collects Millions of E-mail Address Books Globebally
Significance: Hard to say. The "targeted killing program" referred to in the headline is a policy that the entire intelligence community collaborates on. It would be quite unusual if the CIA used another agency to gather signals intelligence on its targets. From previous reporting, we know how closely the NSA and the CIA collaborate on just about everything else. Of interest, though, is the way the NSA helped: targeted cyber penetrations are a very rich source of counter-terrorism intelligence. They don't really just use the phone anymore. The Post withheld a bunch of details, appropriately so, so the significance beyond this bit of trivia is unknown. The other story, on the mass collection of contact lists, is more interesting. It is also, in some ways, a deeper dive into a subject already brought to the surface -- the NSA's global collection of Internet metadata, of which contact lists are a part. The collection falls under the Executive Order that authorizes foreign intelligence collection, so Congress doesn't have as many ways to oversee these programs. The NSA says that these foreign intelligence programs are subject to the same "minimization" procedures if your contact list or mine happens to get caught up in their net.
The Week
Escape your echo chamber. Get the facts behind the news, plus analysis from multiple perspectives.

Sign up for The Week's Free Newsletters
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
Key point: From what we know of the NSA's aperture issues, it's hard to believe that a lot of US persons contact lists haven't passed through NSA filters and servers at some point. It is really difficult to segregate different types of digital information as it passes through filters, cables, nodes and servers around the world.
Explanation: The intelligence committees in Congress know all about the NSA's collection of SIGINT on specific terrorist targets. They are less familiar with "overcollects" of US persons Internet metadata arising from the NSA's global intelligence programs. This ought to be rectified.
What we still don't know: Can the NSA figure out in any efficient way without having a human examine each bit of data what belongs to a US person and what does not, especially if it is collected from a point originating overseas?
Harm to national security from publication: None. In my opinion, which is of limited relevance, these articles do not appreciably harm national security.
A free daily email with the biggest news stories of the day – and the best features from TheWeek.com
Marc Ambinder is TheWeek.com's editor-at-large. He is the author, with D.B. Grady, of The Command and Deep State: Inside the Government Secrecy Industry. Marc is also a contributing editor for The Atlantic and GQ. Formerly, he served as White House correspondent for National Journal, chief political consultant for CBS News, and politics editor at The Atlantic. Marc is a 2001 graduate of Harvard. He is married to Michael Park, a corporate strategy consultant, and lives in Los Angeles.
-
 The environmental cost of GLP-1s
The environmental cost of GLP-1sThe explainer Producing the drugs is a dirty process
-
 Greenland’s capital becomes ground zero for the country’s diplomatic straits
Greenland’s capital becomes ground zero for the country’s diplomatic straitsIN THE SPOTLIGHT A flurry of new consular activity in Nuuk shows how important Greenland has become to Europeans’ anxiety about American imperialism
-
 ‘This is something that happens all too often’
‘This is something that happens all too often’Instant Opinion Opinion, comment and editorials of the day
-
 The recycling crisis
The recycling crisisThe Explainer Much of the stuff Americans think they are "recycling" now ends up in landfills and incinerators. Why?
-
 The L.A. teachers strike, explained
The L.A. teachers strike, explainedThe Explainer Everything you need to know about the education crisis roiling the Los Angeles Unified School District
-
 The NSA knew about cellphone surveillance around the White House 6 years ago
The NSA knew about cellphone surveillance around the White House 6 years agoThe Explainer Here's what they did about it
-
 America's homelessness crisis
America's homelessness crisisThe Explainer The number of homeless people in the U.S. is rising for the first time in years. What’s behind the increase?
-
 The truth about America's illegal immigrants
The truth about America's illegal immigrantsThe Explainer America's illegal immigration controversy, explained
-
 Chicago in crisis
Chicago in crisisThe Explainer The "City of the Big Shoulders" is buckling under the weight of major racial, political, and economic burdens. Here's everything you need to know.
-
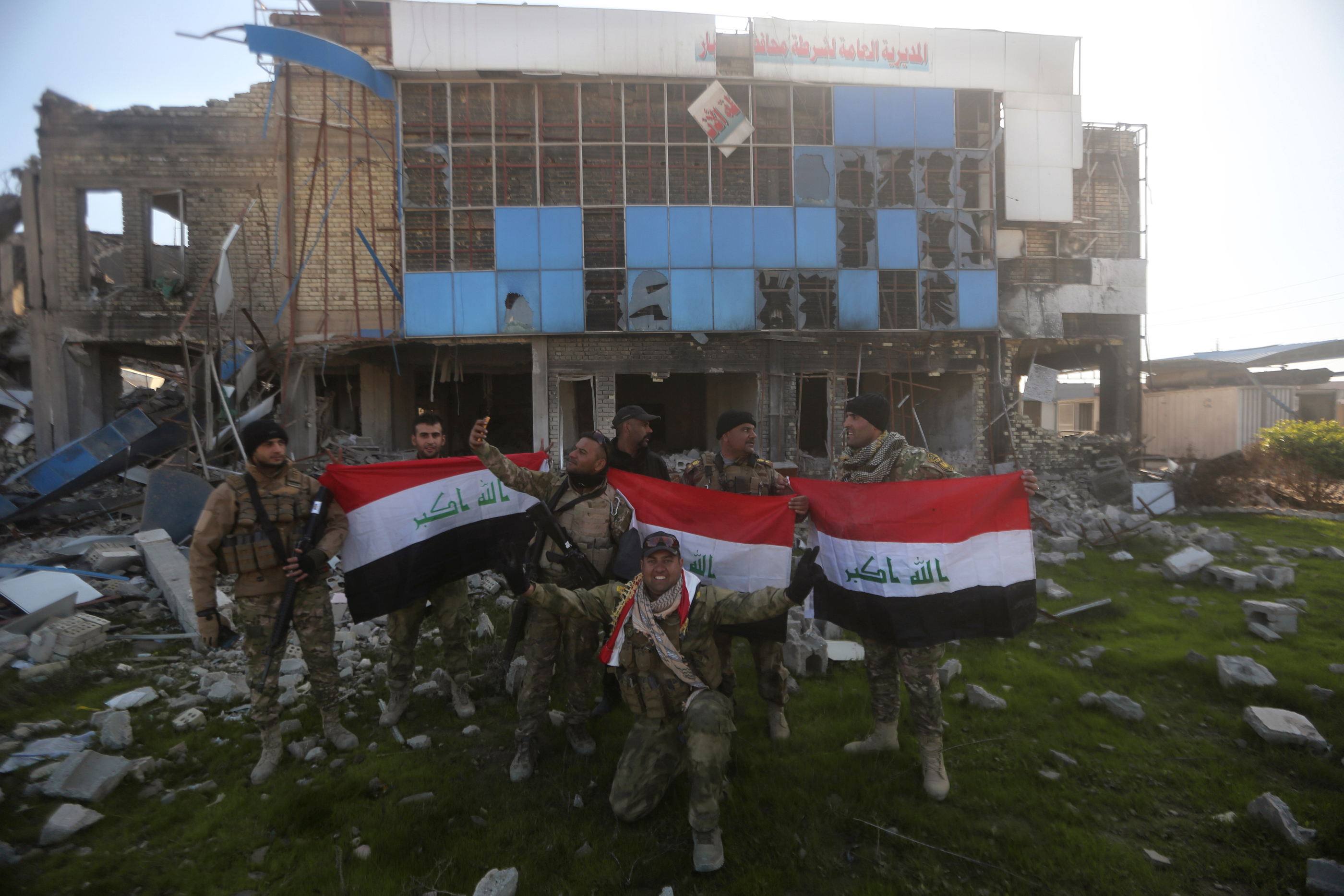 The bad news about ISIS's defeat in Ramadi
The bad news about ISIS's defeat in RamadiThe Explainer The contours of a broader sectarian war are coming into focus
-
 America can still destroy the world
America can still destroy the worldThe Explainer The decline of U.S. military power has been greatly exaggerated
