No, the Zombie Apocalypse has not begun: How hackers infiltrated the Emergency Alert System
Until the EAS is fixed, you may not want to believe everything you hear on the TV or radio

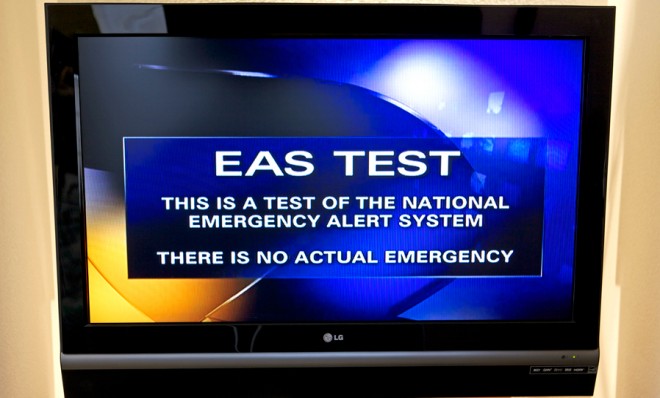
In February, viewers of the Steve Wilkos talk show on CBS affiliate KRTV in Great Falls, Mont., got a rude surprise. First came the discordant tone of the Emergency Alert System — you know the sound, usually signaling a test, no big deal — then came the message, delivered in a somber male voice:
Civil authorities in your area have reported that the bodies of the dead are rising from their graves and attacking the living. Follow the messages on-screen that will be updated as information becomes available. Do not attempt to approach or apprehend these bodies, as they are extremely dangerous.
The EAS was reportedly hacked at local stations in California, Michigan, New Mexico, and Utah, too. And now we know how. On Monday, security firm IOActive announced that Digital Alert Systems — the Monroe Electronics subsidiary that makes decoders allowing local or federal agencies to interrupt your regularly scheduled broadcast to issue a warning — had messed up.
The company released public firmware updates for its DASDEC-I and DASDEC-II emergency-alert decoders/authenticators that included a private root SSH (Secure Shell) key. "This key allows an attacker to remotely log on in over the Internet and can manipulate any system function," said IOActive's Mike Davis. Anyone who discovered this vulnerability and had modest networking skills could issue fake emergency alerts, suppress real ones, or even shut down the system.
The Week
Escape your echo chamber. Get the facts behind the news, plus analysis from multiple perspectives.

Sign up for The Week's Free Newsletters
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
And the DASDEC problem wasn't the only vulnerability in the Emergency Alert System, or even the only one in the Monroe Electronics family. In late June, the U.S. Cyber Emergency Response Team (CERT) said that both DASDEC systems and two others from Monroe, the R189 One-Net and R189SE One-NetSE, have several weak points, the most head-slapping of which is that many broadcasters never changed the default administrative password.
Apparently, it was this last issue — the default passwords — that allowed the zombie apocalypse warnings. Monroe Electronics issued a firmware update to fix the issues on April 24, after the system weaknesses were discovered. IOActive says it waited to publicize its findings until after broadcasters had a chance to update their equipment. But this fix probably isn't permanent, and it probably didn't entirely solve the problem.
"To the best of my knowledge there is still a significant number of vulnerable systems on the Internet that have not patched this issue," says IOActive's Davis. "Additionally, many EAS systems run in a peer-to-peer network so even partial patching of the issue may still result in widespread fictitious EAS alerts." And firmware updates are an important part of the solution, but not the only one. To truly resolve the problem, "re-engineering needs to be done on the digital alerting system side," Davis adds.
The Emergency Alert System — the successor to the Emergency Broadcast System introduced during the Kennedy administration — is an important conduit of emergency information, from hurricane and other extreme weather alerts to child-abduction Amber Alerts and urgent messages from the president. This probably won't be the last time hackers disrupt the system for nefarious reasons or just for a laugh.
A free daily email with the biggest news stories of the day – and the best features from TheWeek.com
Sadly, that means you should evaluate the emergency alerts flashing across your screen, popping up on your smartphone, or blaring out from your radio based on plausibility. If there really is a zombie attack, you'll get some other form of confirmation soon enough — via cable news or the internet, say. Keep that in mind before you load up your shotgun with brain-pulverizing anti-zombie buckshot.
Peter has worked as a news and culture writer and editor at The Week since the site's launch in 2008. He covers politics, world affairs, religion and cultural currents. His journalism career began as a copy editor at a financial newswire and has included editorial positions at The New York Times Magazine, Facts on File, and Oregon State University.

