AT&T 'hacker' Andrew 'Weev' Auernheimer goes to jail: An explainer
A master troll will serve 41 months in prison for what many argue is not even a cybercrime

The internet is going nuts over the 41-month sentence handed down to Andrew 'Weev' Auernheimer, the so-called AT&T hacker who collected and publicly released over 100,000 user email addresses back in 2010. A notorious troll and would-be geek hero, Weev is now due for some serious jail time for what some critics are saying is yet another case of federal overreach against hackers. Here's what you need to know:
Who is this guy?
The 28-year-old is a a self-described hell-raiser. Alex Pasternack at Motherboard describes him as "the world's most notorious troll." In a humanizing profile from last year, Adrian Chen at Gawker calls him a "reviled master troll" who has "spent his life on the margins of cyberspace, a harbinger of online chaos."
The Week
Escape your echo chamber. Get the facts behind the news, plus analysis from multiple perspectives.

Sign up for The Week's Free Newsletters
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.

Weev's exploits on 4chan are notorious. A 2008 New York Times Magazine cover story about him reveals a nomadic troublemaker who has no problem tapping ugly racism or ruining the credit ratings of his enemies to get his way. Weev, on the other hand, sees himself as a crusader for social good who isn't afraid to ruffle the feathers of authorities. And that's how he landed himself in hot water with the feds.
What did he do to AT&T?
In 2010, he and a partner, Daniel Spitler — under the name Goatse Security (NSFW warning if you Google that; it's a troll inside joke) — "hacked" AT&T's website to obtain user log-in info. The pair contend that they were merely exposing a security flaw that could be exploited by someone with more malicious intentions. Here's how The Next Web describes the process:
AT&T wanted to offer a convenient way of letting users log into their 3G data plan accounts, auto-populating users email address on the dashboard by referencing the unique identifier (ICC-ID) of the user's iPad.
[Weev and his accomplice], realizing this, produced a script that utilized brute force techniques to auto-generate thousands of unique ICC-ID's, harvesting email addresses as the script went on.
It's a situation where you can see what AT&T were trying to do, it’s such a shame that most tech-savvy users would recognize how the email addresses were generated. No passwords were stolen but that won’t stop thousands of iPad owners from looking at AT&T with even more of a suspicious eye. [The Next Web]
Weev, who answered questions concerning his case in a Reddit AMA, asserted his actions were politically motivated, and supposedly warned AT&T before releasing the data that it was the company's duty to patch the loophole. AT&T didn't — at least not for a few hours. It was then that Weev leaked the data to Gawker, which ran with the story.
A free daily email with the biggest news stories of the day – and the best features from TheWeek.com
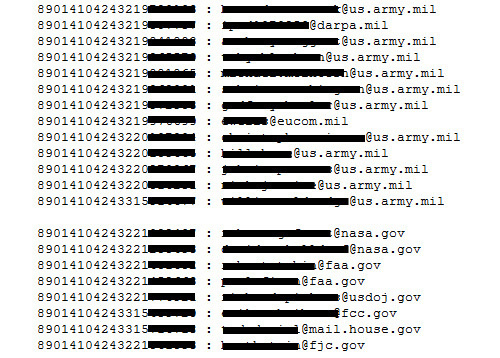
But here's the kicker: The way he obtained the email addresses was arguably legal. Weev cribbed the user data by simply changing letters in the URL, which is available on public servers (he didn't even write the script, which ran for more than a day). "Because Auernheimer didn't illegally access a private server and he wasn't able to gain a list of user passwords — which was confirmed during testimony — the case has drawn much interest from security researchers and online activists," says The Verge.
What are the formal charges, then?
One count of identity fraud and one count of conspiracy to access a computer without authorization.
What is his sentence?
41 months in in prison, followed by three years of supervised release. He'll also have to pay $73,000 in damages to AT&T (which, let's remember, wasn't actually damaged in the incident — just embarrassed). Weev tweeted this shortly before the sentence was read:
And here's what blogger Anil Dash had to say:
What does Weev say in his defense?
Mashable was able to speak with Auernheimer in New York City prior to the sentencing. "I did the right thing," he says in the video below. "I did something of global social good. I'm going to continue to criticize rich and powerful people from inside a jail cell."

