Edward Snowden: 'I care more about the country than what happens to me'

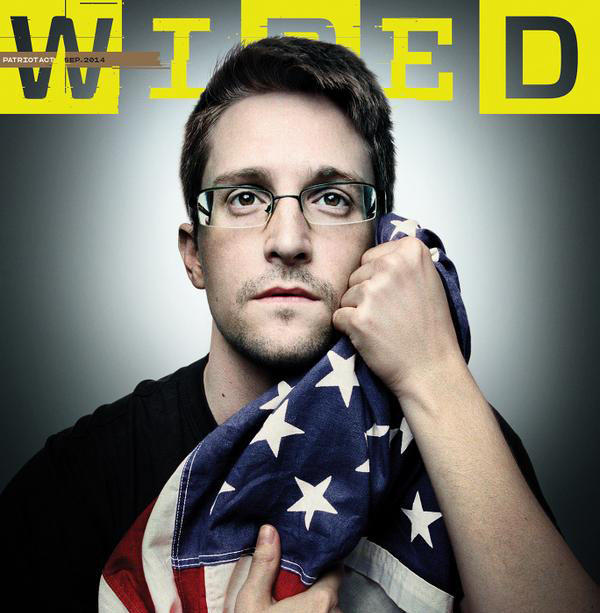
Author and journalist James Bamford recently gained unprecedented access to NSA leaker Edward Snowden, whose temporary asylum in Russia was just extended for three more years. The result is a thorough, exclusive interview published in the September issue of Wired.
According to Bamford, a gaunt-looking Snowden is taking great pains to evade his NSA and CIA pursuers. He limits his contact with outsiders, avoids American-trafficked areas in Russia, and switches computers and email accounts constantly. During their meetings, Bamford wasn't allowed to bring his iPhone because he was warned that "a cell phone can easily be turned into an NSA microphone" even when it is turned off. Despite such vigilance, Snowden believes it's only a matter of time before he is caught. "I'm going to slip up and they're going to hack me. It's going to happen," he says.
But Snowden isn't afraid of jail time, he claims, "so long as it was for the right purpose." He adds, "I care more about the country than what happens to me. But we can't allow the law to become a political weapon or agree to scare people away from standing up for their rights, no matter how good the deal. I'm not going to be part of that."
The Week
Escape your echo chamber. Get the facts behind the news, plus analysis from multiple perspectives.

Sign up for The Week's Free Newsletters
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
Perhaps the most interesting revelations in Bamford's article, however, are about the final events that pushed Snowden to become a leaker. In the spring of 2013, Snowden learned of an NSA program called MonsterMind that hunted for the beginnings of foreign cyber attacks. Unlike similar, competing software, MonsterMind would automatically fire back, with no human involvement. That was a problem for Snowden, Bamford writes:
In addition to the possibility of accidentally starting a war, Snowden views MonsterMind as the ultimate threat to privacy because, in order for the system to work, the NSA first would have to secretly get access to virtually all private communications coming in from overseas to people in the U.S. "The argument is that the only way we can identify these malicious traffic flows and respond to them is if we're analyzing all traffic flows," he says. "And if we're analyzing all traffic flows, that means we have to be intercepting all traffic flows. That means violating the Fourth Amendment, seizing private communications without a warrant, without probable cause or even a suspicion of wrongdoing. For everyone, all the time." [Wired]
Read Bamford's complete interview at Wired.
A free daily email with the biggest news stories of the day – and the best features from TheWeek.com
Lauren Hansen produces The Week’s podcasts and videos and edits the photo blog, Captured. She also manages the production of the magazine's iPad app. A graduate of Kenyon College and Northwestern University, she previously worked at the BBC and Frontline. She knows a thing or two about pretty pictures and cute puppies, both of which she tweets about @mylaurenhansen.

