Why the NSA telephone records program is probably unconstitutional


Judge Richard J. Leon has ruled that the NSA's bulk telephone records surveillance program is probably unconstitutional. Though the judge will allow the government to appeal before he shuts down the program, his ruling is a stinging and often caustic reproach to the government's claims about the nature of its surveillance and the legal basis on which it is conducted.
Leon has several arguments.
He notes that the government insists that only "identifiers" that meet the "Reasonable Articulable Suspicion" standards — specific telephone numbers that have been pre-cleared and pre-approved by NSA supervisors — can be checked against the database.
The Week
Escape your echo chamber. Get the facts behind the news, plus analysis from multiple perspectives.

Sign up for The Week's Free Newsletters
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
But he points out that the nature of the program itself renders this distinction fairly irrelevant. In order for an "approved" query to have any significance whatsoever, every single number in the database has to be checked against it in order to build a foundation of other numbers to begin the call-chaining process. And since the numbers called by the original numbers are NOT approved "identifiers", the "third" hop used by the analysts to discover who THOSE numbers are calling is analogous to the initial "legal" search, except that virtually all of the identifiers have not been pre-cleared or pre-vetted. Yes, the NSA might mind that Terrorist "A" is connected to "Terrorist "B" through several links, but the middle links — which correspond to actual people — can be queried at will, and can be subject to other intelligence analysis activities, like using public databases to discover who the number belongs to.
It may be necessary for the NSA to do build this haystack, but in doing so, it does, on a daily basis, run the dirty or suspect numbers against every record in the database, which means that the records belonging to you are accessed for the sake of comparison regularly.
(Noting that the U.S. insists that the declassified orders do not specify which telephone companies are compelling to provide records, he writes that "the Government has asked me to find that Plaintiffs lack standing based on the theoretical possibility that the NSA has collected a universe of metadata so incomplete that the program could not possibly serve its putative purpose." "Candor of this type," he notes, "defies common sense and does not exactly inspire confidence!")
So, do you have a reasonable expectation to privacy here? It's true that the Supreme Court held in Smith v. Maryland (1979) that metadata in general was not subject to the same level of protection as other personal or personally generated information. The NSA regularly cites this to say that we don't have ANY expectation of privacy whatsoever to metadata, only to content. But Leon notes that collected metadata today is orders of magnitude more intrusive than metadata collected back when the Supreme Court had to figure out whether a police agency could use telephone records for a short period of time to determine the source of harassing phone calls. (That metadata, not incidentally, was destroyed by police; the NSA keeps theirs for five to seven years). Further, the way we "interact" with our phones is much different than it was in 1979. Phones have become inextricable parts of many people's moment-to-moment existence now, and one would assume that if the way we use a technology changes, the privacy implications would change, too, for better or worse, and that would be something the court would have to consider. (Phones are cameras. Phones are weapons. Phones are books. Etc.)
A free daily email with the biggest news stories of the day – and the best features from TheWeek.com
Further, Leon notes that this program is an institutionalized intelligence gathering mechanism, a formerly secret one, set up between the powerful state and several powerful companies. An individual, single police action it ain't.
Does the government have a compelling enough interest to justify these privacy violations? Leon concludes that they haven't made that case. There is no important government interest that would be placed in jeopardy if the program were adjusted to require some sort of individualized suspicion to be articulated, he writes, and the government never produced evidence that the program had stopped an imminent terrorist attack that a program with more safeguards would not have.
Marc Ambinder is TheWeek.com's editor-at-large. He is the author, with D.B. Grady, of The Command and Deep State: Inside the Government Secrecy Industry. Marc is also a contributing editor for The Atlantic and GQ. Formerly, he served as White House correspondent for National Journal, chief political consultant for CBS News, and politics editor at The Atlantic. Marc is a 2001 graduate of Harvard. He is married to Michael Park, a corporate strategy consultant, and lives in Los Angeles.
-
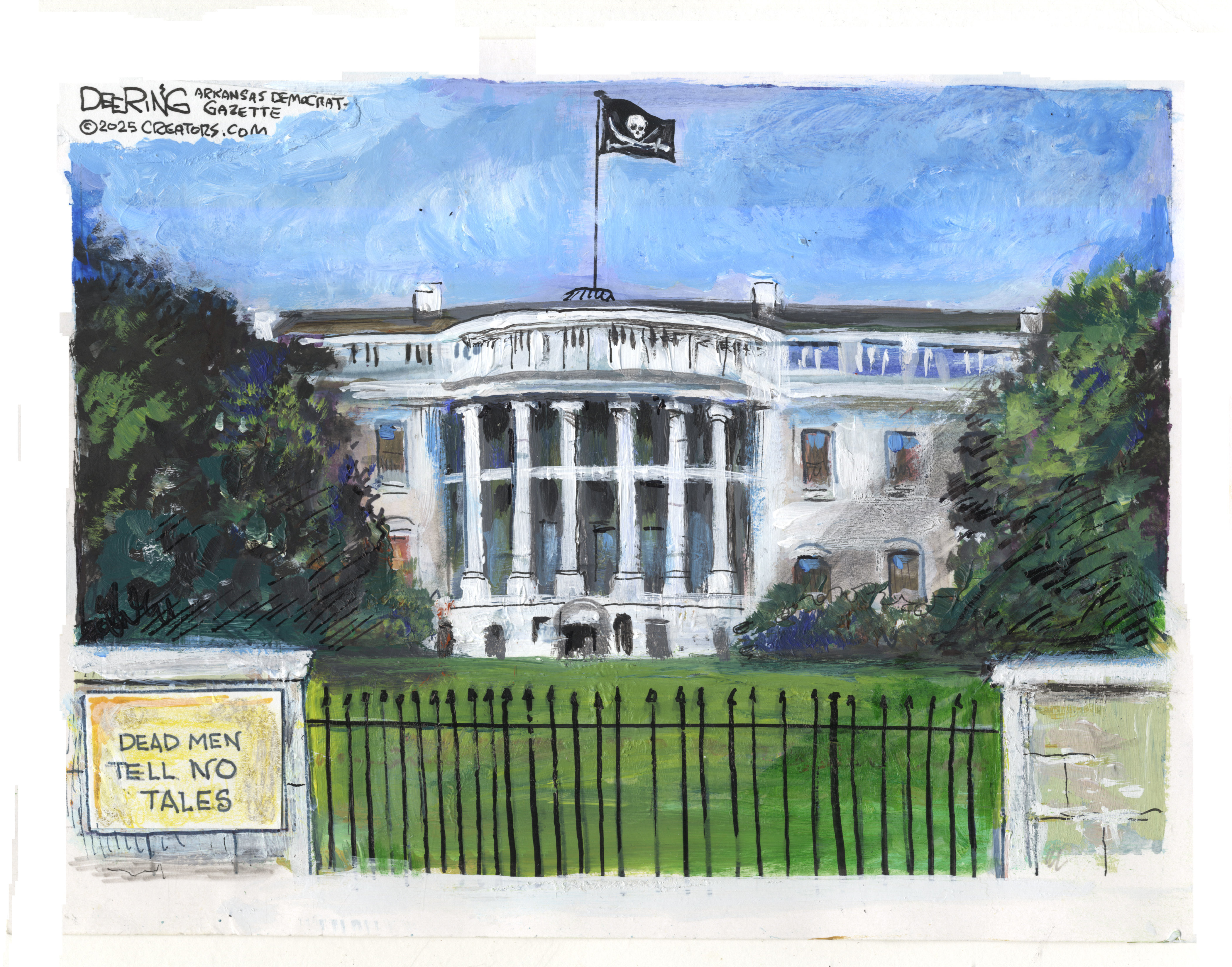 Political cartoons for December 14
Political cartoons for December 14Cartoons Sunday's political cartoons include a new White House flag, Venezuela negotiations, and more
-
 Heavenly spectacle in the wilds of Canada
Heavenly spectacle in the wilds of CanadaThe Week Recommends ‘Mind-bending’ outpost for spotting animals – and the northern lights
-
 Facial recognition: a revolution in policing
Facial recognition: a revolution in policingTalking Point All 43 police forces in England and Wales are set to be granted access, with those against calling for increasing safeguards on the technology
