How the NSA got hacked
I showed newly leaked malware to a government cyber leak plugger. Here's what I discovered and what might come next.


On Monday, a group of hackers dubbing themselves the Shadow Brokers took to the web with an audacious offer: For 1 million bitcoin, they would hand over an archive of potent computer cracks they hinted had come from inside the National Security Agency.
To prove that their bounty was real, they shared several examples. These included programs that, if executed correctly, would allow programmers to connect to far-afield computers, bore deep holes through virtual firewalls, and steal secrets without leaving so much as a spare bit behind.
As companies like Cisco scrambled to test the exploits, the security community responded with incredulity and alarm: Had the NSA been hacked? Was there yet another mole, a new Edward Snowden, who had walked out of the agency with a thumb-drive full of classified source code?
The Week
Escape your echo chamber. Get the facts behind the news, plus analysis from multiple perspectives.

Sign up for The Week's Free Newsletters
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
From our morning news briefing to a weekly Good News Newsletter, get the best of The Week delivered directly to your inbox.
The answer, according to Snowden himself, and at least one of the intelligence officials assigned to protect the agency's secrets after his leaks agrees, is that a nation-state — probably Russia — covertly hijacked an internet node used to help manage the agency's empire of intelligence-collecting implants in computers across the globe. That — or there's a new mole.
In the weeks and months after Snowden's disclosures began to shake loose the agency's secrets, teams within the intelligence community scrambled to assess the damage and salvage as many tools and capabilities as they could.
One urgent task: Shore up vulnerabilities in the way that the NSA's hackers — specialists, engineers, and scientists working in the Remote Operations Center (ROC) inside of the agency's Tailored Access Operations (TAO) division — interacted with their intelligence targets — usually computers and servers — across the globe. Snowden's documents showed that the NSA could break into a number of popular commercial products. They did not provide the source code showing exactly how the NSA managed to do this. So building physical and virtual firewalls around these specific tools became a top priority for dozens of NSA employees.
Imagine a forest of secrets to protect, and a frenzied effort by rival intelligence agencies to burn down as much of the greenery as possible. The most valuable — the tallest trees — include the locations of surreptitious taps, the identities of human, governmental, and commercial partners and sources, and the specific vulnerabilities in encryption the NSA had found and how they were exploited. Among the trees on the fringe of the fireline: mundane but valuable computer scripts used in everyday computer network operations.
A free daily email with the biggest news stories of the day – and the best features from TheWeek.com
A former intelligence official with direct operational knowledge of TAO and who worked from the outside the agency with some of its damage assessment teams reviewed the scripts for The Week and recognized many of them as genuine.
They did come from the NSA, the official said. Like everyone interviewed for this story, the official insisted on anonymity in exchange for providing a candid assessment of the situation.
This official believes that there are two possibilities. One is that a disgruntled insider — or a new whistleblower, styling himself like Edward Snowden — "simply walked out of the ROC with a thumb drive."
Another is that the secrets dribbled out of the NSA for years, and a country with sophisticated clandestine cyber capabilities had been waiting at the right point on the internet to collect them.
According to Top Secret budget documents leaked by Snowden, TAO teams control more than 85,000 implants hidden in computers and servers all over the world as well as the complex pathways that exfiltrated the data collected by these implants and transmitted the digital "take" back to the NSA for processing and analysis.
A typical TAO target might be a Russian think tank that provides strategic advice to President Vladimir Putin. Most computers used by employees at that organization have nothing that the U.S. intelligence community would want to see. But a small fraction would. Instead of asking a human asset to break into the building and install a cyber bug on all of its computers, TAO's ROC would find devices on the gateway on the network — often a commercial firewall — and hack through them, installing code that sniffs through all the traffic the server handles, looking for keywords and selectors that might be of interest.
Several documents released by Snowden listed the manufacturers of firewalls, operating systems, and control mechanisms the NSA managed to compromise. Some of these backdoors the NSA might have purchased directly from companies using secret agreements overseen by the agency's National Commercial Solution Center. Others were no doubt found by NSA developers themselves; whether they were shared with the companies whose products were compromised was a decision made above the heads of those that found them. Others were stolen by the NSA from foreign intelligence services that had discovered them.
To get into the targets — "boxes," the NSA calls them — ROC operators at "op stations" inside Ft. Meade, and in field stations in Georgia, Hawaii, and Texas, set up covert nodes on the regular internet to launch the attacks. To protect the locations of these agency-owned and operated nodes, the ROC operators launder their attacks through other computers. These are called "redirectors."
As Snowden tweeted on Tuesday, the agency's hackers are taught not leave footprints of their work on those computers; this would be clear evidence to foreign intelligence agencies that the NSA was using them.
"It's not like the NSA can build a second internet to transfer the copies of the main one. But the capacity to move this data around exists," a NSA consultant said. "You need to do it so it isn't recorded or billed for it."
Finding anonymous launch points is expensive and time consuming. That's why the same redirector might be used for hundreds of different operations.
"Sometimes, it'll be a firewall just copying data and sending it out. Sometimes it's much more complex," the intelligence official familiar with TAO's processes said.
If a foreign intelligence agency managed to "own" one of these redirectors, it could silently record all of the tools that the ROC hackers were using, collecting and archiving them. Intelligence officials and operators with knowledge of the cyber collection process say that the NSA understands that its exploits are sometimes hijacked, and that its redirectors might be discovered. (It has, in the process of defending America's cyber infrastructure, discovered many Chinese and Russian command and control computers that are used to penetrate American networks.)
According to several experts who have analyzed the source code, the Shadow Broker bundle contains exploits for firewalls, instructions to implant a backdoor into the memory of the device, and a number of self-deleting execution commands.
The files' explanatory language used leaves little doubt that the tools are used by the NSA. One of the tools, Apache_Setup.text, specifically directs a specified disk image to the "IP of redirector" and speaks of "getting ops station back to normal" after the trick is performed. The signature of the code is identical to commands and formats known to be used by the NSA.
Why would Russia release these tools now?
It's tempting to link the release directly to the leak of Democratic National Committee e-mails earlier this summer — and that leak all but dares observers to conclude that Russia was trying to shake up the U.S. presidential election. The dates associated with the scripts and signatures of the more recent leak suggest that the country (and the hackers) have had them for a while — at least since 2013. After an entity known as Guccifer 2.0 released the DNC information, anonymous officials inside the government publicly attributed the hacks to the Russian government. The evidence, they said, was clear.
Snowden, for his part, said that Russia might have used the new malware leak to warn the U.S. away from attributing specific cyber operations — including the DNC attack — to their government. "This leak looks like a somebody sending a message that an escalation in the attribution game could get messy fast," he tweeted.
Another theory — one that is gaining some traction among experts outside the government — is that the Shadow Brokers release is the Russian response to an unknown-to-the-public U.S. government cyber operation against their country, one launched in retribution for the DNC hacks.
An administration official contacted Wednesday would not confirm that the NSA's tools had been stolen. But, this official said, "in cases like these, we would probably not do anything or say anything." What this official means, I think, is that the U.S still has the biggest and best covert SIGINT architecture in the world and maintaining that global dominance, rather than retaliating for specific transactions, is the preferred policy. At least in public.
A third option, one offered by the former intelligence official who worked with TAO: Perhaps the Russian want to simply induce panic inside the NSA. The exposure of these tools might lead TAO to burn accesses, which could give the Russians the means to map where and how the agency launched its operations from. (The NSA likely understands this, and will probably avoid acting in a way that would reveal any more of their covert infrastructure.)
At least two of the exploits point to previously unknown firewall vulnerabilities for Cisco and Fortinet products. The relationship between these companies and the NSA — already damaged by the Snowden revelations and subsequent disclosures — will get worse. "If NSA knew several years ago that its hacking tools were stolen, not notifying Cisco and other vulnerable U.S. firms would be outrageous," tweeted Christopher Soghoian, the principal technologist with the Speech, Privacy, and Technology Project at the American Civil Liberties Union.
But there might be a saving grace to this otherwise damaging leak. As valuable as these "endpoint" tools are, the tools used to break through routers and switches that form the "midpoints" of the global internet architecture haven't been among those released.
At least not yet.
Marc Ambinder is TheWeek.com's editor-at-large. He is the author, with D.B. Grady, of The Command and Deep State: Inside the Government Secrecy Industry. Marc is also a contributing editor for The Atlantic and GQ. Formerly, he served as White House correspondent for National Journal, chief political consultant for CBS News, and politics editor at The Atlantic. Marc is a 2001 graduate of Harvard. He is married to Michael Park, a corporate strategy consultant, and lives in Los Angeles.
-
 31 political cartoons for January 2026
31 political cartoons for January 2026Cartoons Editorial cartoonists take on Donald Trump, ICE, the World Economic Forum in Davos, Greenland and more
-
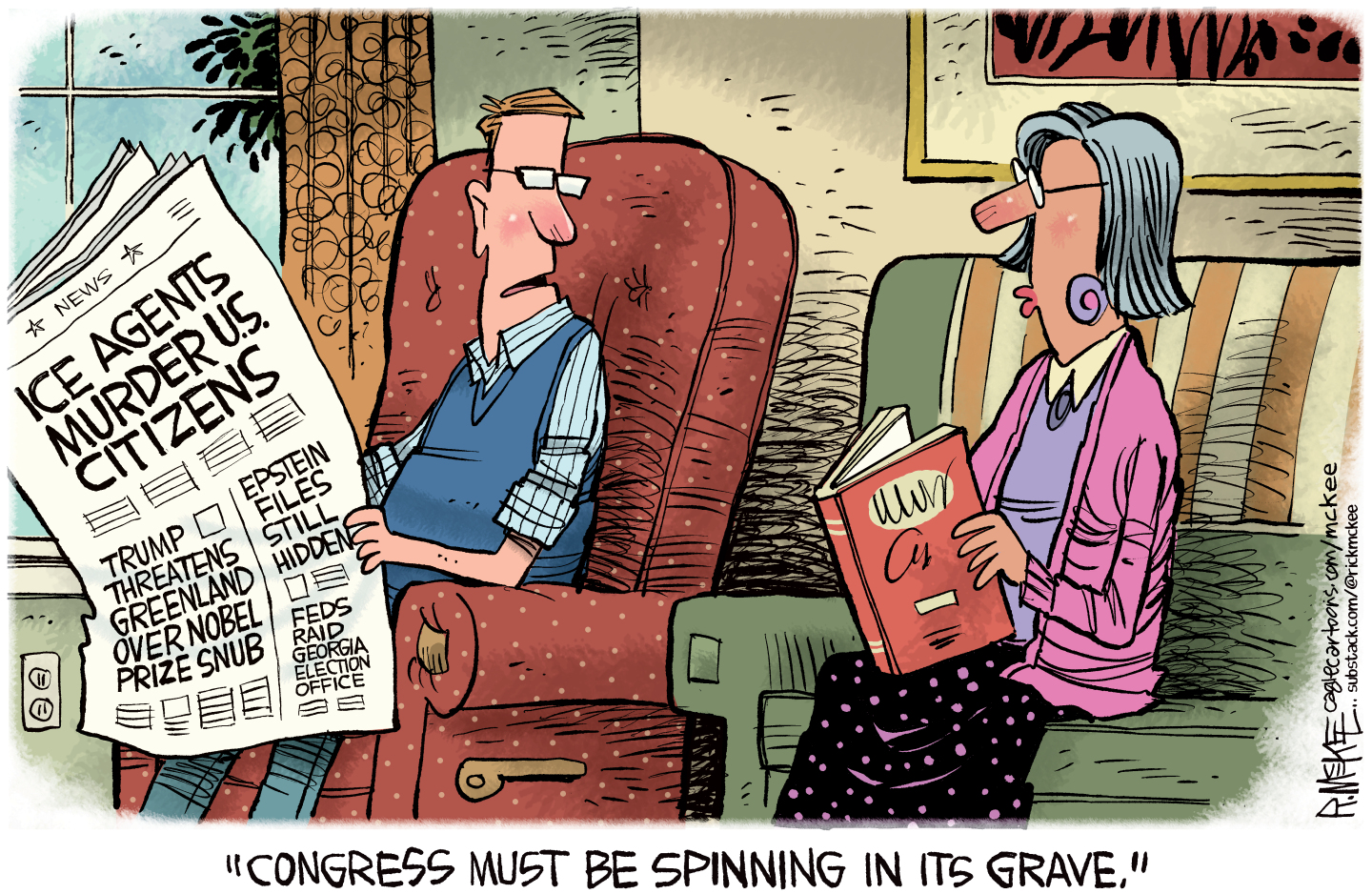 Political cartoons for January 31
Political cartoons for January 31Cartoons Saturday's political cartoons include congressional spin, Obamacare subsidies, and more
-
 Syria’s Kurds: abandoned by their US ally
Syria’s Kurds: abandoned by their US allyTalking Point Ahmed al-Sharaa’s lightning offensive against Syrian Kurdistan belies his promise to respect the country’s ethnic minorities
-
 How do you solve a problem like Facebook?
How do you solve a problem like Facebook?The Explainer The social media giant is under intense scrutiny. But can it be reined in?
-
 Microsoft's big bid for Gen Z
Microsoft's big bid for Gen ZThe Explainer Why the software giant wants to buy TikTok
-
 Apple is about to start making laptops a lot more like phones
Apple is about to start making laptops a lot more like phonesThe Explainer A whole new era in the world of Mac
-
Why are calendar apps so awful?
The Explainer Honestly it's a wonder we manage to schedule anything at all
-
 Tesla's stock price has skyrocketed. Is there a catch?
Tesla's stock price has skyrocketed. Is there a catch?The Explainer The oddball story behind the electric car company's rapid turnaround
-
 How robocalls became America's most prevalent crime
How robocalls became America's most prevalent crimeThe Explainer Today, half of all phone calls are automated scams. Here's everything you need to know.
-
 Google's uncertain future
Google's uncertain futureThe Explainer As Larry Page and Sergey Brin officially step down, the company is at a crossroads
-
 Can Apple make VR mainstream?
Can Apple make VR mainstream?The Explainer What to think of the company's foray into augmented reality
